IT security, accountability and auditability are critical today. Securing vCenter Server using auditable identities, for instance via an Active Directory identity source, is likely common for most vCenter consumers. This ensures individual access can be used to audit actions back to an admin as well as provide higher security through strong password policies and the absence of a shared account credentials, such as the SSO administrator.
Something that can be overlooked is the security of the ESXi hosts themselves.
There are multiple options for securing your ESXi hosts, one being the use of lockdown modes and limited user access, restricted management network access, or a combination of them both.
In this blog post I want to show you a simple way to configure your hosts to use an Active Directory group to control user access to an ESXi host.
This is achieved by editing the value associated with an advanced setting - ‘Config.HostAgent.plugins.hostsvc.esxAdminsGroup’.
One prerequisite to achieving this is that the hosts must be domain joined. Information on how to do this can be found here.
Editing this on a handful of servers is easy enough if you are doing it manually, but who wants to be manually typing or copying & pasting this?
I have put together a PowerShell Function that can simplify the editing of this setting for single hosts, or on mass to all ESXi hosts that you have connected your PowerCLI session to.
The code can be found on GitHub here.
Here are two examples of how it can be used -
1Set-ESXiHostAdminGroup -Target single -Entity esxi01 -Group "infrastructure_admins"
2
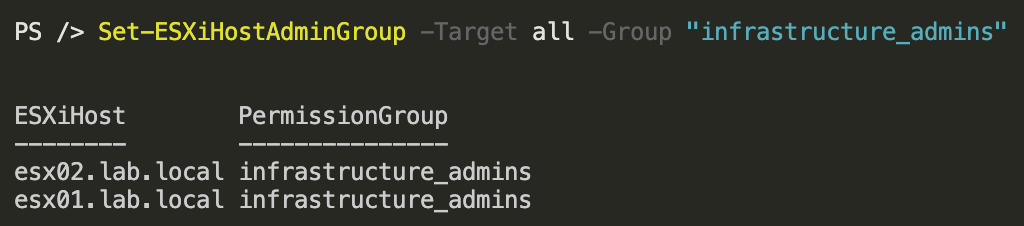
3Set-ESXiHostAdminGroup -Target all -Group "infrastructure_admins"
For the purposes of this demo, I will update all ESXi Hosts within my vCenter instance using the second example. You could edit the function to target clusters if you wish.
Setting before -
1Set-ESXiHostAdminGroup -Target all -Group "infrastructure_admins"
After -
You will need to wait the length of time defined in this setting until being able to log in -
Now all users that are in the 'infrastructure_admins' Active Directory group will be able to log into the ESXi host with administrator permissions using their AD credentials.
Hope this has been useful, thanks for reading!